What are the Best Practices to ensure API Security!


An Application Programming Interface, commonly known as API, refers to an intermediary that enables the exchange of information between two independent software components/platforms and ensures that the information reaches the right place. An API acts as a mediator between the external and internal software functions; making the information exchange process as seamless as possible. It not only offers protocols, tools, and routines to software app developers but also allows one to extract and share data in an accessible way.
APIs are indispensable in the realm of software development, but at the same time are highly vulnerable to attacks by hackers who exploit them for malicious gains. External APIs have public-facing endpoints and are susceptible to hacking; while internal APIs can be improperly accessed or misused. Since APIs interact with your web or mobile apps, securing them should be your priority.
This post outlines the adverse effects of API security breaches as well as the best practices to follow for ensuring API security.
What are the consequences of an API Security breach?
API security breaches often expose confidential data belonging to an Offshore Software Firm or their clients. As such, one such instance may result in the affected business enterprise losing credibility and encountering dire circumstances. Several such incidents have made headlines in recent years risking the reputation of firms and ushering in global security risks.
Take a look at some instances of API breaches and their repercussions.
· The audio chat app, Clubhouse experienced an audio spill when an unauthorized user was successful in connecting to the API to enter multiple chat rooms, and then accessed audio files and thereafter, shared those files to a third-party platform. As a result, Agora, their API provider witnessed a sharp fall in their client shares.
· British Airways encountered an API breach in the year 2018. Information belonging to 380,000 customers was stolen directly from payment forms and the airways had to pay a fine of more than 183 million pounds as a result of this hack.
· In 2021, the Central Bank of Russia alerted firms about a scam where hackers stole information from mobile banking apps and then used it to execute fraudulent monetary transactions. The attackers debugged banking apps, examined the payment order, and studied the architecture of remote banking API calls to find out the victims’ bank account numbers.
· Recently, an API exposure concerning Facebook photos resulted in a data breach affecting 6.8 million users. The attackers took advantage of a login bug to access users’ photos. This scam led to a fall in Facebook’s share prices.
Established Practices for ensuring API Security
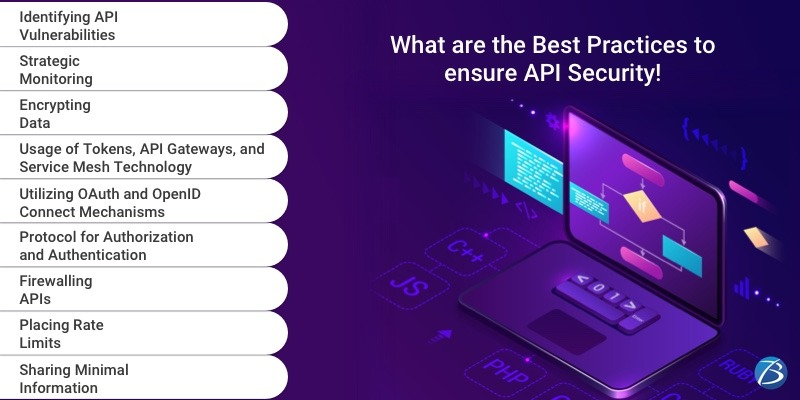
Identifying API Vulnerabilities
For securing your API against security threats, you must first identify the parts of the API lifecycle that are vulnerable to security risks. But, this task becomes quite challenging as software companies may use thousands of APIs at a time. The best ways to detect the security loopholes are scanning for the incorrect code and conducting extensive testing.
Strategic Monitoring
Monitor consistently and be ready to troubleshoot whenever any error is detected. For this, you need to audit, log relevant information on the server, and maintain that history as long as it is logical in the matter of your production servers’ capacity. In case any issues crop up and you need to debug; your logs need to be turned into resources. Monitoring dashboards can also be used for tracking your API consumption. Remember to add the version in the paths of all APIs. This will allow the functioning of several APIs of various versions and also enable the retiring and deprecation of one version over the other.
Encrypting Data
All data should be encrypted employing TLS (Transport Layer Security) and signatures should be made mandatory; for ensuring that only authorized users can access, decrypt, and modify data.
The usage of Tokens, API Gateways, and Service Mesh Technology
The usage of tokens is a sound API security practice. Access tokens enable an application to access your API. An access token is provided after the completion of the processes of authentication and authorization. Using these tokens, you can build trusted identities and then assign tokens to those identities for controlling access to the API.
An API gateway acts as a single point of entry for all API calls. A good gateway enables enterprises to not only authenticate API traffic but also analyze and control how APIs are used.
The service mesh technology employs yet another layer of control and management by routing requests from one service to the subsequent one. A service mesh optimizes the combined functioning of all these moving parts and also establishes proper access control, authentication, and other security measures.
Utilizing OAuth and OpenID Connect Mechanisms
It’s a good idea to delegate the task of authorization and authentication of your APIs utilizing OAuth and OpenID Connect.
Using OAuth you need not have to remember endless passwords and rather than opening an account on each website, you can connect via the credentials of a third-party provider. OAuth allows clients to get secured delegated access to the server resources on behalf of the resource owner. This mechanism is leveraged by biggies such as Google, Amazon, Facebook, Twitter, and Microsoft.
Coming to APIs, the API provider depends on a third-party server for managing authorizations. So, the consumer, instead of providing their credentials, provides a token obtained from the third-party server. This way the consumers’ credentials are not exposed thereby securing them, and the API providers need not worry about protecting the authorization data since they receive only tokens.
OAuth is used as a delegation protocol for conveying authorizations while OpenID Connect is an identity layer added on top of OAuth for offering additional API security and authentication.
Protocol for Authorization and Authentication
Several APIs are easily discoverable making them an easy target for hackers. This issue can be resolved by following the practices listed below.
· Guard your API documentation via authorization credentials for controlling the number of API requests and the persons who can access them.
· Try not to make APIs user-friendly because hackers often impersonate users and make use of descriptive error messages to intrude into the API.
Firewalling APIs
Firewalling works wonders in protecting APIs. API security is arranged into two layers as follows.
· The first layer: This layer is in DMZ, with the API firewall for executing basic security mechanisms that include checking the size of messages, HTTP layer-related security, and SQL injections. This enables blocking intruders during the early stages. This message is then forwarded to the second layer.
· The second layer: This layer is in LAN and contains advanced security mechanisms on the content of data.
Placing Rate Limits
The higher the popularity of an API, the greater are its chances to encounter malicious attacks like DDoS. DDoS attacks are executed by sending continuous calls until the server crashes. However, setting rate limits is an ingenious way to prevent such attacks on an API and to control the issues that adversely affect its performance. A rate limit controls how often an API can be called. Moreover, placing a rate limit throttles unauthorized connections as well.
Sharing Minimal Information
Check out the best practices on how to share minimal information.
· Make sure that you display the minimum required information, particularly in error messages.
· Lock content and email subjects to pre-defined messages which cannot be customized.
· IP addresses may disclose locations and so it’s better to maintain their secrecy.
· IP Blacklist and IP Whitelist can be used to restrict attackers from accessing your resources.
· Separate access into various roles, limit the number of administrators, and hide sensitive information across all interfaces.
Bottom Line:
I hope this post has conveyed how important it is for business organizations to incorporate API security practices. If you are looking for an IT firm for assistance concerning API security, picking an efficient and experienced Offshore Software Development agency would be a wise decision.
To know more about our core technologies, refer to links below:
Other articles and publications:
Articles and publications of other companies:
- +1 (469) 277-0804
- 8305 Tripoli Trl, Frisco, TX 75034, United States
- www.biz4solutions.com/






